TRAVEO™ T2G Automotive Body Controller - FAQ – BOOT AND SYSTEM CALL - KBA232509
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Home Page: TRAVEO™ T2G Automotive Body Controller - FAQ – CDC
14. Boot and System call
14.1. How can I check if IRQ0/IRQ1 is configured properly, if SROM API or System call is not working?
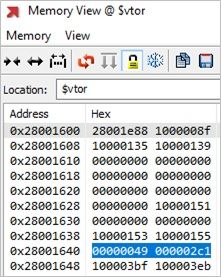
SROM APIs are executed by Arm® Cortex®-M0+ core in interrupt context using IRQ0 and IRQ1. So, proper interrupt handler addresses and priorities need to be configured for IRQ0 and IRQ1.The required interrupt handler addresses reside in ROM memory and can be found at locations 0x40 and 0x44, respectively.
For more details, see section 3.1 Setting Up IRQs for System Calls in AN220242 Flash Rewriting Procedure for Traveo II Family.
The following are the required configurations:
- Assign proper interrupt handler addresses for IRQ0 and IRQ1.
- IRQ0 and IRQ1 on Cortex-M0+ core must enable CM0P_SCS_ISER (Bit0 and Bit1 on 0xe000e100 must be
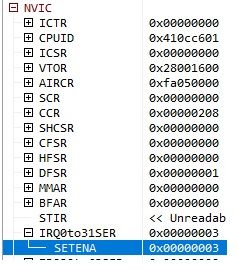
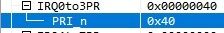
set to 1). - Set the IRQ0 priority on CM0+ core to 1 (CM0P_SCS_IPR0: the value on 0xe000e400 must be set to 0x00000040). Assign proper priorities for both interrupts. Priority of IRQ0 must be less than the priority of IRQ1. Lower the priority number, higher is the priority. For instance, 0 has the highest priority while 7 has the lowest.
- Do not map any other interrupt on IRQ0 and IRQ1 of CM0+.
- For all other interrupts present in the CM0+ core, assign a priority that is less than the priority of the two interrupt lines (IRQ0 and IRQ1).
- Make sure the CPUSS_CM0_PC1_HANDLER address matches the IRQ0 vector address.
- First 2 KB of SRAM is used as Protected SRAM for system calls. DeepSleep should retain this part of SRAM.
Follow these steps to check if the configuration is correct:
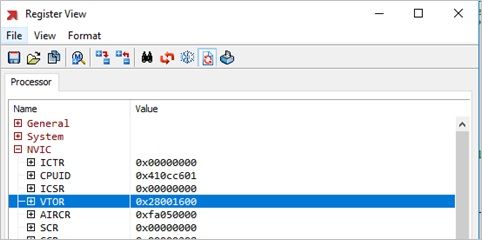
- Check the value of address in VTOR register in CM0+ register set.
- Check the memory pointed by VTOR+0x40 and VTOR+0x44 and the addresses of 0x40 and 0x44 and make sure the values match.
- Check if IRQ0 and IRQ1 (CM0P_SCS_ISER: Bit 0 and Bit 1) on the CM0+ core is enabled (CM0P_SCS_ISER: Bit 0 and Bit 1 are 1).
- The value of CM0P_SCS_IPR0 register is 0x00000040. For CM0+, configurable priority levels range from 0 to 3. Based on the register value, the priority number of IRQ0 is 1 and priority of number of IRQ1 is 0. Hence, check if the priority of IRQ0 is lesser than the priority of IRQ1.
- Ensure that CPU interrupt is enabled on CM0+ core based on the PRIMASK register value. PRIMASK value needs to be “0”.
14.2. How do I program the eFuse memory?
You can program the eFuse memory using the ‘Blow Fuse Bit’ system call. See Section 33.6, “eFuse Memory” in the Traveo™ II Automotive Body Controller Entry Family Architecture Technical Reference Manual (TRM) (002-19314 Rev. *E). This should be used only on the customer bits (AddressOffset 0x68 to 0x7F). You need to pass the following three parameters to this system call:
- Macro Address = AddressOffset% EFUSE_NR
- Byte Address = AddressOffset/EFUSE_NR
- Bit Address = Bit position in the byte
EFUSE_NR is ‘4’ for CYTx devices.
14.3. Can the flash operations be cancelled after initiating?
The Erase Suspend can used to suspend only in non-blocking mode. In the blocking mode, the system call will exit only after the completion of erase; so it cannot be suspended. If EraseSector is called on a sector other than the suspended one, the new sector will be erased and the suspended sector will be in an unknown state. EraseSector can be called on the suspended sector to restore to blank state.
Program Row system does not have suspend mechanism similar to erase operation. In the blocking mode, the system call will exit only after the completion of programming. In non-blocking mode, the programming will happen in the background and cannot be suspended.
14.4. Which part of the SRAM can be used for the internal bootloader?
Bootloadable application start address must be within a valid RAM memory length - [RAM_START + 3 KB, RAM_END – 6 KB]. Bootloadable application length must be a value for which the bootloadable application image fits into a RAM address range [RAM_START + 3 KB, RAM_END – 6 KB].
14.5. Can CySAF be used in NORMAL protection stage to perform authentication?
Yes, it is possible to authenticate the application in the NORMAL protection state using CySAF and configuring TOC2_FLAGS.APP_AUTH_CTL as 2 Though the authentication is disabled, the valid public key should be programmed to SFlash.
14.6. How can the start address of an application be relocated during startup after reset?
- For boot address, change of a single application can be achieved by changing SFLASH_TOC2_FIRST_USER_APP_ADDR.
- FBL is placed at 0x10000000 and Flash Boot will always try to jump to this address, by default, since this is application start address is specified in TOC2. If you need to switch this jump between two locations, you need to configure two application addresses in TOC2 and implement Flash Boot Authentication. If one application is corrupted, Flash boot jumps to the other. For this, you need to make use of Secured Boot and CySAF based applications.
14.7. Can System Call of Cy_FB_VerifyApplication be used as a standalone (that is. without SLLD)? In this case, is the Public key same as the key used in Flash boot?
Cy_FB_VerifyApplication is part of Flash Boot Shared Functions, so it can be used without SLLD. See the section 34.2.1 Flash Boot Shared Functions of the Traveo II Architecture TRM.
Also, the Public key is same as the key used in Flash boot.