Code Examples Forum Discussions
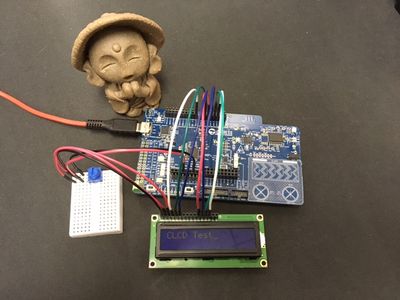
Hi,
While ago, we had a discussion asking for charLCD sample for PSoC 6.
https://community.cypress.com/t5/PSoC-6-MCU/Display-LCD-on-PSOC-6/m-p/266274
And to my surprise, I could not find a charLCD component for PSoC 6 in PSoC Creator.
Adding on top this, the querist was showing 5V LCD in the block diagram,
so I suggested that he needs to use a 3.3V version to go with PSoC 6.
And if I had stopped there, I felt somewhat flighty, so I ordered "my" 3.3V LCD.
The good news is the parts arrived pretty soon,
but the bad news was I could not afford time to fight with it.
Finally, today, here is my first sample of charLCD like LCD control sample.
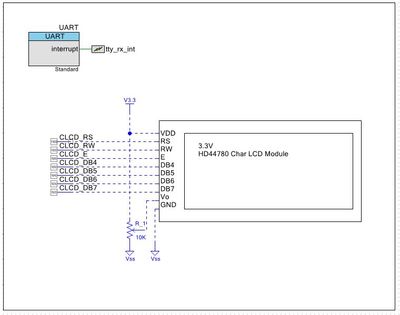
The schematic
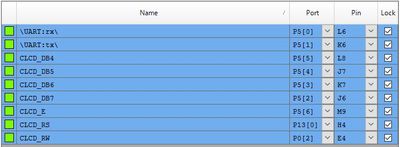
The Pins
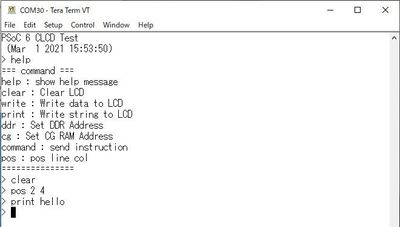
Tera Term log
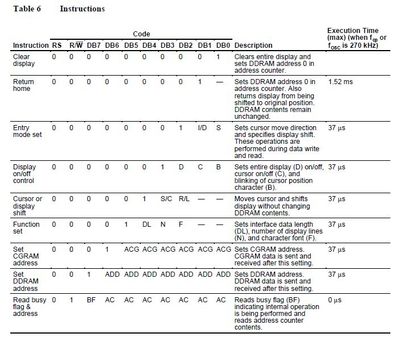
For the command(s) please refer to the instruction of HD44780U Datasheet
Note: Sorry, I did not implement "read" function.
1-Mar-2021
moto
14-Oct-2021 Attached project updated
(1) Added delay before initializing the LCD
(2) When DB7 is high in writing, clear DB7 after write phase is done to prevent the program from hang.
Show Less
Secure boot is a boot process that ensures that only authenticated code is executed on the device. Secure booting typically involves authenticating the application flash images using a key-based security protocol defined by a market/application specific standard. In this code example, we will see how to configure the firmware to perform Secure Boot in TRAVEO™T2G MCU using IAR Embedded Workbench for ARM® (EWARM).
After reset, the ARM® Cortex® M0+ CPU starts executing from ROM boot. ROM boot validates SFLASH. After validation of SFLASH is complete, execution jumps to Flash boot and configures the DAP according to the protection state. The Flash boot then validates the first application present in the TOC2 structure and jumps to its entry point if it is valid. If the SFLASH or first application is found to be invalid or corrupted, the device will enter a DEAD protection state and stays in the DEAD protection state until the device is reset.
In this example, the TRAVEO™ T2G MCU's Flash Boot, which is first verified by ROM boot and guaranteed to be secure, verifies the CM0+ firmware. After booting, the CM0+ firmware verifies the CM4 firmware and enables only if the verification is successful. The board used in this example is CYTVII-B-E-1M-SK which consists of TRAVEO™ T2G CYT2B7 Series MCU. The code was developed in IAR Embedded Workbench for ARM® (EWARM) with Sample Driver Library (SDL).
Scope:
This code example demonstrates how to implement Secure Boot in TRAVEO™T2G MCU using the Sample Driver Library (provided by Infineon) and IAR Embedded Workbench for ARM® (EWARM).
Implementation:
For Secure Boot implementation, the device lifecycle stage must be transitioned to SECURE (where SFLASH rewriting is prohibited). Transition to SECURE life cycle stage is done by blowing secure eFuse bit. Before moving the device to SECURE life cycle, you need to update the TOC2, public key in the SFLASH region in NORMAL_PROVISIONED lifecycle stage.
- Update Linker Scripts: Use the linker script “linker_directives_tviibe_rev_d.icf” provided in the zip file which contains required sections for the secure boot implementation.
- TOC2 Configuration: The TOC2 is prepared as a constant table cy_toc2 in the main_cm0plus.c file, and must be placed at the specified address (0x17007C00) in the SFLASH. The following elements shall be configured in TOC2 :
- .cm0pappAddr1 : Address of the application to be verified by Flash Boot. In this example, the address of CM0+ firmware is specified.
- .cm0pappFormat1 : The format of the application. To make it verified by Flash Boot, this should be set as CYPRESS™ Standard format.
- .shashObj : This specifies the number of SFLASH regions which is verified by ROM boot when the device life cycle stage is SECURE or SECURE_W_DEBUG. To make the device SECURE, value should be atleast 3. The three elements are public key (located at 0x17006400; specified at .sigKeyAddr), SWPU objects (located at 0x17007600; specified at .swpuAddr), and TOC2 itself (located at 0x17007C00; specified at .toc2Addr).
- Asymmetric key preparation: Firmware authentication is done by verifying the digital signature populated at the end of the image as per the CYPRESS™ Standard format. Since digital signatures are generated using asymmetric private keys and verified using public keys, a set of asymmetric keys shall be prepared first.
- In this example, we will use RSA-2048 public and private keys. Copy the files provided in the zip file to the $Installation_Directory$\T2G_Sample_Driver_Library_7.8.0\tviibe1m\src directory of the SDL library.
- A batch script rsa_keygen.bat is included in utils folder which can generate the key pair and converts the public key to C structures. This batch script uses OpenSSL whose version is higher than 1.0.2, to generate RSA keyset, and also requires Python 3.x.x to convert RSA public key to C structures.
- Placing public keys in SFLASH: The public key for verifying the firmware should also be populated in the SFLASH (0x17006400). Copy the public key generated (modulus and exponent) from utils\keys_generated\rsa_to_c_generated.txt to the constant table cy_publicKey in main_cm0plus.c file.
- CYPRESS™ Secure Application Format (CySAF) header: All the application code to be verified must be in CySAF format. File’s main_cm0plus.c and main_cm4.c contains its CySAF header as a table called cy_si_appHeader.
- Adding digital signatures to the application: After building the project, the digital signature should be embedded to the generated elf file using private key. The batch scripts “SB_CM0+.bat” and “SB_CM4.bat” are provided in the zip file use cymcuelftool.exe to add digital signature. In IAR IDE Workspace, include these batch scripts in the post build command line. In IDE, navigate to Project -> Options -> Build Actions -> Post Build Command line and select the corresponding batch files provided in the zip file for the respective cores i.e., SB_CM0+.bat and SB_CM4.bat.
- Booting CM0+ firmware: Once the elf file with the correct digital signature is flashed, the CM0+ firmware should be verified by Flash Boot and the CM0+ application starts executing.
- Verifying CM4 firmware: CM4 firmware verification must be implemented by the user. In CM0+ application, the CM4 firmware is verified by using Flash Boot Shared function Cy_FB_VerifyApplication(). Please refer the section 38.2.1 of the Technical Reference Manual for the function description. If the verification is successfully, the CM4 application starts executing.
- After code compilation, perform the following steps to program the device:
- Connect the Starter kit to your PC using the USB cable through the KitProg3 USB connector.
- Program the CM0+ and CM4 applications using Download option in IAR IDE.
Observation:
After programming, there will be two LEDs (LED 1 and LED 4) blinking at a different rate once CM0+ and CM4 applications are verified successfully. LED4 starts to blink after CM0+ application is verified successfully by the Flash boot. LED1 starts to blink after CM4 application is verified successfully by the CM0+ application.
In case of failure of verification of CM0+ application, the LED4 will not blink and further the CM4 application verification will not be done. So, both the LEDs will not be blinking. In case of failure of verification of only CM4 application, the LED1 will not be blinking. If the CM0+ application verification is not successful, CM4 application authentication doesn’t happen.
Summary:
- The device life cycle must be transitioned to SECURE for Secure Boot.
- We have seen how we can implement Secure Boot in TRAVEO™T2G MCU using IAR Embedded Workbench for ARM® (EWARM).
Attached is a code example for the TC397 Application Kit
Hi all,
Kindly find the attached updated infineon firmware that work at LIN 9600 baudrate. You may need to just download and start working application code without updating or changing in LIN stack.
Best Regards,
Rohit Rawat
Show LessTo emulate the optical encoder, the design uses two PWM peripherals. Each PWM peripheral uses a TCPWM block in the PWM mode. The output frequency of both PWMs is the same but they are 90° out of phase. The PWM peripherals are configured to generate signals at 15.625Hz.
To detect the direction of rotation, a quadrature decoder peripheral is used. This peripheral uses a TCPWM block configured as a quadrature decoder. The counter of the quadrature decoder is initialized with a midpoint counter value on an index event. The counter value increases or decreases based on the quadrature input signal. For example, a positive edge on phiA increments the counter when phiB is 0 and decrements the counter when phiB is 1. Therefore, if phiA leads phiB, the counter value of the quadrature decoder increases; if phiB leads phiA, the counter value decreases. Based on the current and the previous counter values the direction of rotation is determined. Digital output pins drive the LEDs.
See TRM 25.3.3 Quadrature Decoder Mode for more details about the Quadrature Decoder Configuration.
Test environment:
- SDL version 7.9.0
- IAR version 9.30
CPU Board:
- CYTVII-B-E-1M-176-CPU Board
- CYTVII-B-E-BB Board
Dependency:
- CYTVII-B-E-1M-176-CPU board should be connected on CYTVII-B-E-BB board.
- Connect a jumper wire from PWM_phiA (P2.10) output to phiA (P2.16) QuadDec input.
- Connect a jumper wire from PWM_phiB (P10.6) output to phiB (P10.5) QuadDec input.
Provided below is the SerialRx v0.0 component implementing simple command line interface between UART Terminal and PSoC microcontroller.
Using this component, human-readable UART Terminal messages can be easily received and processed by the microcontroller. Component is, in essence, a software library, which splits the incoming stream of bytes into individual control messages using standard termination characters.
Component features:
* Compatible with PSoC4 SCB UART and PSoC5 UART
* Optional external or internal interrupt mode
* Standard \n and \r termination characters
* Optional Comma, Space and Tab separators
Component can be useful for process control or parameters update, such as: PID tuning, setting control voltages, PWM frequency, etc. Component is compatible with Creator 4.0 and Creator 4.4, and was tested using CY8KIT-059 PSoC5LP Prototyping Kit and CY8KIT-044 PSoC4M Pioneer Kit. Demo projects are provided.
Attached archive contains component library, component datasheet and several demo projects for PSoC4 and PSoC5. Please read installation instructions in the readme.pdf.
Credits:
Bob Marlowe (Cypress, ret.)
Figure 1. PSoC4 SCB UART basic project schematic using SerialRx. The Component receives messages from the Terminal and turns RGB LED on/off. Both SCB UART and SerialRx are configured for internal interrupt mode.
Figure 2. Terminal window showing command messages and PSoC4 responses. Recognized commands ('R_ON') are executed with confirmation echo sent back ('>R_ON'). Unrecognized commands ('foo') are ignored and an error status is reported ('!foo').
Provided below is the Goertzel64 v0.0 component, which is a fixed-point implementation of an optimized Goertzel digital filter. Using this component allows to detect the amplitude of a single tone in the digital data stream.
Component features:
* Compatible with PSoC4 and PSoC5
* Implements optimized Goertzel filter
* 64-bit fixed-point implementation
* optional Hanning window
Component was developed for DTMF (touch tone) decoding. It can be used whenever single frequency amplitude must be estimated in the data stream, such as harmonics detection in the power line, sound equalizer, CTCSS (tone squelch), Morse code or FSK decoder.
Component is compatible with Creator 4.0 and Creator 4.4, and was tested using CY8KIT-059 PSoC5LP Prototyping Kit and CY8KIT-044 PSoC4M Pioneer Kit. Demo projects are provided.
Attached archive contains component library, component datasheet and several demo projects for PSoC4 and PSoC5. Please read installation instructions in the readme.pdf.
Figure 1. Project schematic for filter performance test. Custom DDS and 32-bit fixed-point Square Root components are supplemented to produce a single tone and extract a magnitude of the tone form the filter output power.
Figure 2. Filter performance test: Red – normalized magnitude output, Blue – normalized power (magnitude squared). Filter input – 16-bit sine; filter length 64, filter target frequency 1 kHz, sampling rate 8 kHz. Left scale - dB, bottom scale – tone frequency, Hz.
Figure 3. Filter performance with Hanning window enabled: Red – normalized magnitude output, Blue – normalized power (magnitude squared). Filter input – 16-bit sine; filter length 64, filter target frequency 1 kHz, sampling rate 8 kHz. Left scale - dB, bottom scale – tone frequency, Hz.
Figure 4. Filter tone envelope extraction demo: Red trace– normalized magnitude output; Blue – input signal (strobed tone). Filter input – PWM modulated sine of 1019 Hz. Filter settings: 8-bit data width, filter length 64, target frequency 1 kHz, sampling rate 8 kHz. Scales: Left – amplitude, Bottom – data block index.
smartconx_target@Q!w2e3r4t5y6u7i8o9p0||/t5/%E4%BE%8B%E7%A8%8B/TC3xx-SCR%E5%8A%9F%E8%80%97/td-p/670224
Show LessDescription:
- This example demonstrates TCPWM use case with CC0 and Period Auto Reload with switch event.
- One TCPWM will generate interrupt every second. In the interrupt handler, it will change the period buffer and cc0 buffer and enable the switch event.
- One LED will blink at the period 1 second, another LED will change the blink frequency and duty cycle.
Test environment:
- CYTVII-B-E-1M-SK(Traveo II starter kit board)
- SDL version 7.9.0
- IAR version 9.30
ModusToolbox users may run into errors like “OpenSSL SSL_read: Software caused connection abort, errno 113” while running github.com-related git_clone/git_fetch in ModusToolbox. It means your connection to github.com is blocked for some reason.
ModusToolbox的用户在执行与github.com相关的git_clone/git_fetch等操作时,可能会遇到错误:“OpenSSL SSL_read: Software caused connection abort, errno 113”。这通常是因为你到github.com的连接被神秘力量屏蔽了的缘故。
In this case, you can turn to use some third-party repo_relaying servers, like ghproxy.com, to bypass the restrictions. Basically, you need to run the following GIT_config command to make it work in ModusToolbox:
这时你可以使用一些第三方的repo中继服务器(譬如mirror.ghproxy.com),来绕过这个限制。基本上,你需要运行如下这个GIT_config命令来使得这个中继服务器被ModusToolbox接受:
git config --system url."https://mirror.ghproxy.com/https://github.com".insteadOf https://github.com
The tool is designed to help you with that. It automatically locates your ModusToolbox and adds the value, and then handles the conflicting settings.
这个工具被设计用来帮助你完成这个工作。它会自动定位你的ModusToolbox并添加这个设置,然后处理与之相冲突的一些设定。
Click to download the tool [source] (or directly use this link)
Click to download the tool [mirror] (password: mtbs)
Latest version / 最新版本:v0.1.7.5
Guide
- Download the latest release and unzip it wherever.
下载最新的版本,然后随便找一个位置解压它。 - Run the file Install.cmd.
运行Install.cmd这个文件。 - Reboot ModusToolbox and done.
重启ModusToolbox,就可以了。 - Run the file Uninstall.cmd to remove the settings. You may uninstall the tool before you update it as well.
运行Uninstall.cmd这个文件可以移除本工具造成的更改。更新本工具之前也最好先卸载。 - Try clear the cache of ModusToolbox first every time you encounter an error. A lot of git error stay once they occurred. Follow this link to do this.
如果你遇到错误,请先清理缓存再进行下一步操作,每一次都是。因为很多git的错误如果发生了,那它们将一直残留,除非你清理过缓存。依照这个链接的提示来清理缓存。
Notes
- ghproxy.com is a third-party service that can be unstable.
ghproxy.com是一个第三方的服务,它可能不够稳定。 - ghproxy.com is adopted in the tool but not part of the tool. Visit ghproxy.com for more info and support.
ghproxy.com在本工具中被使用,但它不是本工具的一部分。访问 ghproxy.com 来获取更多信息,并支持它。 - Support ModusToolbox 2.x and hopefully later.
兼容ModusToolbox 2.x和后续的版本(可能)。 - The tool only helps you restore accessibility to the GitHub content of ModusToolbox. If you need to use any other content of ModusToolbox (when the variable CyRemoteManifestsOverride is touched by you), you have to uninstall it first or you might see more issues coming.
本工具只帮助你恢复对在GitHub上的ModusToolbox内容的访问。如果你需要使用在其他位置的ModusToolbox内容(此时你通常会修改CyRemoteManifestsOverride变量),你应先卸载本工具,不然你可能会遇到更多的问题。 - The tool is provided AS IS. There is NO WARRANTY.
这个工具是照原样提供的。它不提供任何保证。 - Windows might prevent the scripts from executing. You might see some red warnings about the limit during the execution. Visit this link for lifting the limit.
Windows可能会阻止本工具运行。运行本工具时你可能会看到一些关于此限制的红色警告信息。访问这里了解如何移除这个限制。
\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\\
The tool above is for Windows only. When using Linux/macOS, it's better you add the configuration yourself:
上述工具只能在WIndows下使用。如果你使用的是Linux/macOS,更推荐你自行添加这些配置:
Open a terminal in Linux/macOS.
在Linux/macOS中打开一个命令行窗口。
Run the following command to add the git config in the terminal.
在该命令行窗口中运行下方命令添加这个git配置。
git config --global url."https://mirror.ghproxy.com/https://github.com".insteadOf https://github.com
Then add the environment variable CyRemoteManifestOverride to the system. For ModusToolbox 2.2 and later, set it to the following value:
然后添加环境变量CyRemoteManifestOverride到系统中。对于ModusToolbox 2.2或之后的版本,把该变量设成下方的值:
https://gitee.com/dreamscaperia/mtb-super-manifest/raw/master/mtb-super-manifest-fv2.xml
For ModusToolbox 2.1 and earlier, set it to the following value:
对于ModusToolbox 2.1或之前的版本,把该变量设成下方的值:
https://gitee.com/dreamscaperia/mtb-super-manifest/raw/master/mtb-super-manifest.xml
You can refer to KBA230953 for how to do it in Linux/macOS. And you may refer to this article for how to set it permanently in Linux.
你可以参考KBA230953来了解如何在Linux/macOS中设置环境变量。你还可以参考这个文章来了解如何在Linux中永久设置这个环境变量。